Getting My Sniper Africa To Work
Excitement About Sniper Africa
Table of ContentsFacts About Sniper Africa Revealed5 Simple Techniques For Sniper AfricaWhat Does Sniper Africa Mean?Not known Details About Sniper Africa The Basic Principles Of Sniper Africa Sniper Africa Fundamentals Explained9 Simple Techniques For Sniper Africa

This can be a specific system, a network location, or a theory triggered by a revealed vulnerability or patch, information regarding a zero-day manipulate, an anomaly within the security information collection, or a demand from in other places in the organization. As soon as a trigger is recognized, the searching initiatives are focused on proactively looking for abnormalities that either prove or refute the theory.
Sniper Africa Things To Know Before You Buy
This procedure might include making use of automated tools and queries, together with hand-operated evaluation and relationship of information. Unstructured searching, additionally referred to as exploratory hunting, is an extra flexible approach to threat searching that does not count on predefined criteria or theories. Rather, hazard hunters utilize their expertise and intuition to look for prospective threats or susceptabilities within a company's network or systems, usually concentrating on areas that are perceived as risky or have a history of protection incidents.
In this situational strategy, risk seekers utilize hazard intelligence, along with other pertinent data and contextual information concerning the entities on the network, to recognize potential hazards or susceptabilities connected with the scenario. This may entail making use of both structured and disorganized searching techniques, in addition to partnership with various other stakeholders within the organization, such as IT, lawful, or company teams.
The Ultimate Guide To Sniper Africa
(https://soundcloud.com/lisa-blount-892692899)You can input and search on danger knowledge such as IoCs, IP addresses, hash values, and domain names. This procedure can be integrated with your safety information and occasion administration (SIEM) and threat knowledge tools, which make use of the intelligence to hunt for threats. An additional wonderful resource of knowledge is the host or network artifacts offered by computer emergency reaction groups (CERTs) or details sharing and evaluation facilities (ISAC), which might enable you to export automatic signals or share key info about brand-new attacks seen in other companies.
The very first step is to recognize proper teams and malware strikes by leveraging global detection playbooks. This strategy frequently aligns with risk structures such as the MITRE ATT&CKTM framework. Here are the activities that are most typically associated with the procedure: Use IoAs and TTPs to recognize danger stars. The hunter assesses the domain, atmosphere, and strike actions to produce a theory that aligns with ATT&CK.
The goal is locating, determining, and then isolating the threat to protect against spread or proliferation. The hybrid threat searching strategy integrates all of the above techniques, allowing safety and security experts to personalize the search.
Not known Incorrect Statements About Sniper Africa
When operating in a protection operations center (SOC), hazard hunters report to the SOC supervisor. Some essential skills for a good threat hunter are: It is essential for threat hunters to be able to connect both vocally and in writing with terrific clearness about their tasks, from investigation completely with to searchings for and recommendations for remediation.
Information breaches next and cyberattacks price organizations numerous bucks yearly. These tips can help your company much better find these dangers: Danger seekers need to sort via anomalous tasks and recognize the real hazards, so it is important to understand what the typical functional tasks of the organization are. To achieve this, the threat hunting team works together with vital employees both within and outside of IT to gather important info and understandings.
8 Simple Techniques For Sniper Africa
This procedure can be automated making use of a modern technology like UEBA, which can reveal regular operation problems for a setting, and the individuals and machines within it. Threat seekers utilize this approach, obtained from the military, in cyber war. OODA stands for: Regularly collect logs from IT and safety and security systems. Cross-check the data against existing details.
Determine the appropriate strategy according to the event status. In instance of a strike, perform the case reaction strategy. Take steps to avoid comparable strikes in the future. A hazard hunting team ought to have sufficient of the following: a danger hunting team that includes, at minimum, one knowledgeable cyber risk seeker a basic danger searching framework that gathers and arranges safety occurrences and occasions software program designed to determine abnormalities and locate aggressors Danger seekers use remedies and tools to discover suspicious tasks.
8 Easy Facts About Sniper Africa Shown
Unlike automated hazard detection systems, hazard hunting depends greatly on human instinct, enhanced by sophisticated tools. The risks are high: A successful cyberattack can lead to data violations, financial losses, and reputational damage. Threat-hunting devices offer protection groups with the insights and abilities needed to remain one action ahead of assailants.
Sniper Africa Fundamentals Explained
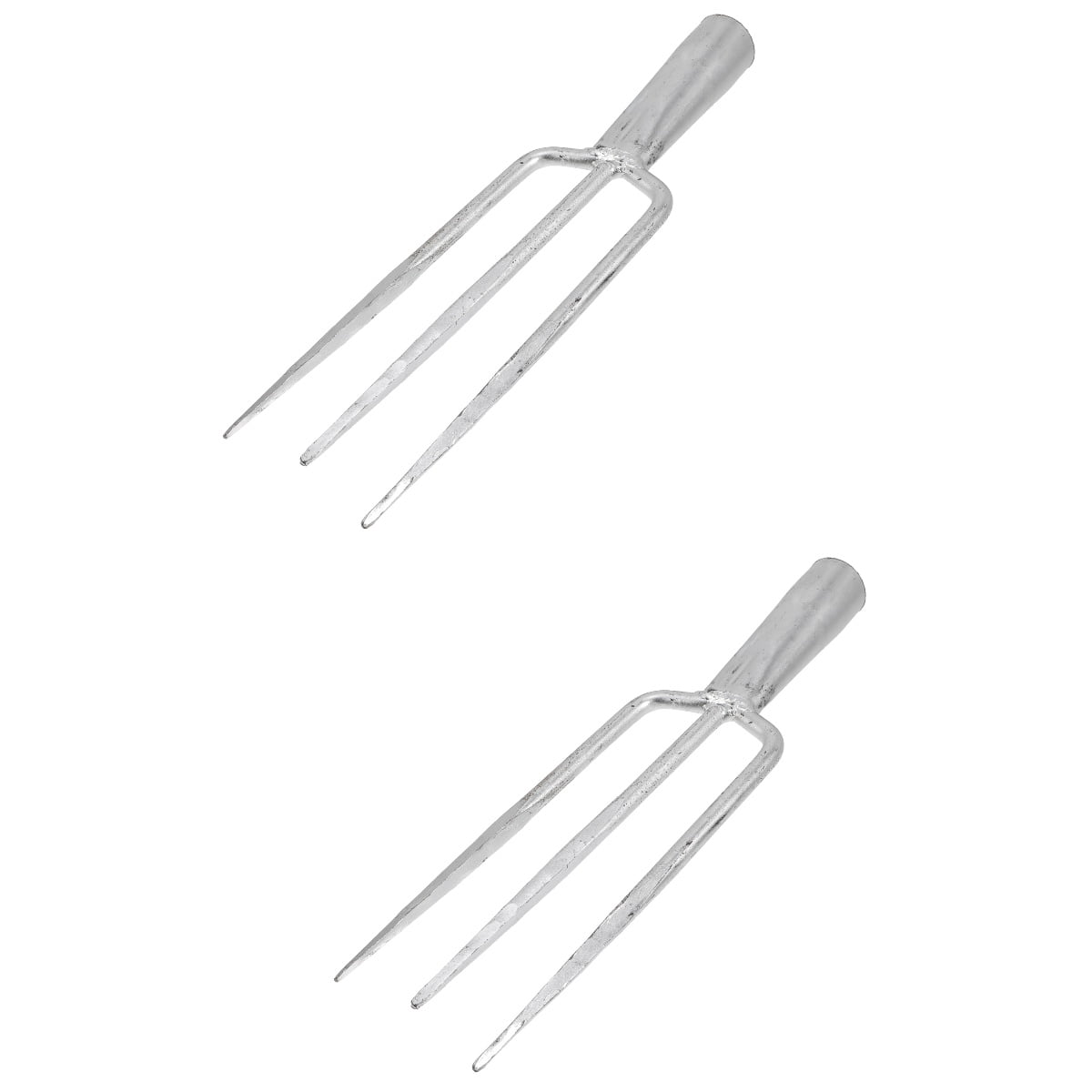
Here are the trademarks of efficient threat-hunting tools: Continual monitoring of network website traffic, endpoints, and logs. Seamless compatibility with existing security facilities. hunting jacket.